Introduction
There is a lot of buzz about Claim based Authentication. In this article, we’ll understand what is Claim based Authentication? What are the benefits and lot more.This is first Postin this Series. In subsequent posts, We will the implementation and more scenarios.
Let’s first understand, what is the need of Claim based authentication?
Problems with Current Authentication Mechanism
As we used to make several user accounts at several portals/websites. So every time we need to access the corresponding website, we need to remember usrename and password and if somehow we forget the password then we need to remember some specific details like security question etc to get the access of the account again. And every time we might not remember all these details. Also It is never advisable to write your user credentials physically.
One more problem, Most of the applications are using some authentication mechanism mainly Classic UserName and Password. As most of developers are not really security experts they use to leave loopholes during development which are easy to break. So it is a major security risk.
Most of developers have some or other day have worked SingleSignOn feature. It’s not always been a simple task. It leads a lot of challenges and many issues after the application is deployed on UAT/Production.
As a user, we create a new user credentials (username and password) to lot of many application on internet like facebook, yahoo, gmail etc and some in-house site like some college portal etc or some enterprise application. So create every time a new credentials and to remember all these credentials and all are secured enough is very tedious. If there is any error you might loose some credentials and could end up in a big loss.
Solution
Imagine the situation where you just need to have one user credential ie username and password and that is enough to access all your portals/websites. This will be Ideal situation. Might be it could not take place completely, but we are somehow moving in this direction.
But how can this take place?
Actually Now a days when we create a Application which has authentication page, we need to understand, how it works. Actually when user logs in an Identity is assigned to that session and that Identity is maintained throughout the session until user logs out or it expires. So let’s view the current scenario.
Means every application which has some authentication mechanism first authenticates the user and gives an Identity and then user gets the rights to access the application. So somehow if we can externalize the authentication part from the application then this will be very helpful and the same authentication application used by several application. I explain it pictorially
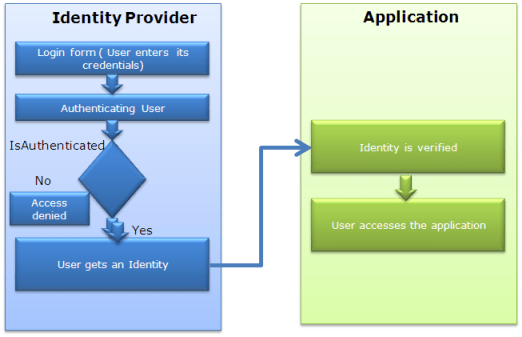
So the basic Idea is, If there are some applications that do the authentication and provides the Identity (Called Identity Provider), and applications rely on this Identity. Like in our daily life

Above picture explains everything about itself.
Claim Based Authentication
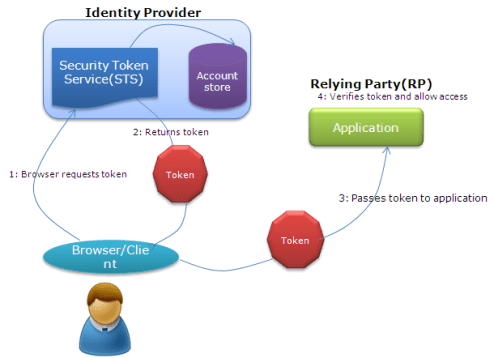
The same mechanism is also followed in Claim based Authentication. There are some authentication provider/Identity provider which are used by various applications so whenever a user tries to access some application, Application checks whether user is authenticated or not, if not, it forwards the user to Identity provider which actually authenticates the user, gives a token to user and forward the user to application. Application verifies the token and user is allowed to access the application.
But this is not so easy in web scenario. There are few challenges – Who are the Identity Providers? – What all the data is needed to the relying party ie what data can be transferred from Identity provider and in which form – If there are multiple Identity providers. How application trust on them.
Actually there are couple of Identity providers nowadays like Google, facebook, WindowsLive Id and many more.. And even we can develop our own Identity provider for on premise applications. This also can be used on Cloud as well.
Now if I am making an application and my application uses some Identity provider to authenticate a user. Then application must understand the token of that Identity provider and also there must be trust relation between application and Identity providers, so that application can rely on the token sent by that Identity provider.
Basics of Claim based Authentication
Now let us discuss what are the basic things involved in it. These are mainly Identity, Tokens, Claims, Identity Provider or Security Token Service, RP (Relying Party) etc. To move ahead we need to understand all these. Lets discuss one be One.
What is an Identity
You can say Identity is a group of information that can uniquely identify anything. Most of the other things also have identity like your own PC, Vehicle etc. But here as we are talking about person. So in this digital era, we can say a digital identity is a group of information to identify a person.
Token and Claims
When this digital identify is passed over wire. It is passed as stream of bytes and that is known as token. Token contains some set of Information about the user in the Claim format. A token can contain multiple claims and every claim contains some specific information. The token is digitally signed so that it can be verified at receiver end. So we can show the pictorially as

Sometimes token be XML based Security Assertion Markup Language (SAML) format. But now application use rather simpler token call as Simple web Token( SWT). So the benefit is here we just not pass user credential but also we can pass some other information of the user to the application.
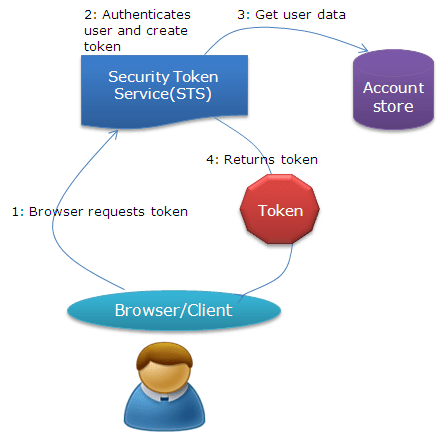
Identity Provider and STS
Identity provider is the key in this technology, this is actually authenticate the user and create the token with claims, as per the requirement and digitally sign it before sending. Identity provider is also known as Security token service. So how STS work lets have a view.
RP (Relying Party)
Relying party are the applications those uses these Identity Provider for authentication. They just need to understand and verify the token and get all the data from the token itself which is required. But before all this, RP needs to build a trust relationship and tell the Identity provider what all data needs for a user. So that next time a token it receives, it can verify the issuer and get the required data.
Complete Scenario
Now you guys got all the basic information about Claim based Authentication. Now let us have a look, how these Identity provider is used
So this is the basics of the Claim based Authentication and in my Next Post we’ll focus on Implementation part with the help Windows Identity Foundation WIF.
Do share your views about this post and let me if I have missed anything.
Cheers,
Brij
Pingback: Claim based Authentication and WIF : Part 2 « Brij's arena of .NET
Hi Brij,
how is it possible to invalidate/reject a token after creation?
regards,
Serge
To invalidate the token, you need to signout. This will remove the token and the user will be treated as unautheticated, This will send the user again to STS. You can write the code as
var authModule = Context.ApplicationInstance.Modules["WSFederationAuthenticationModule"] as WSFederationAuthenticationModule;
authModule .SignOut(true);
So this code will invalidate the token and will force the the user to authenticate again. You can use it as per your requirement.
Pingback: Claim based Authentication and WIF : Part 3 « Brij's arena of .NET
great article, I’ve been trying to wrap my head around this actually just this week; this has been very helpful!
When you say “Next Post we’ll focus on Implementation part with the help Windows Identity Foundation WIF” will this describe the part where you say “But before all this, RP needs to build a trust relationship and tell the Identity provider what all data needs for a user.”
because it isn’t clear from the last illustration how this relationship works…
Have you gone through other post as well and still have some confusion? Do let me know if there is any?
Brij I am going to start my work on using ADFS. I hope your article is really helpful. Will email you if there is any doubt.
Sure.. Will be glad to help you..
really really nice for the one will be working on the same at the initial level, it clears all the concepts.
Gr8 Article it describes everthing what i was looking for a couple of week.
Thanks!!
Glad that you find it helpful!!
gr8 article, keep it up.
Pingback: Reading Notes 2013-06-17 | Matricis
Pingback: Claim based Authentication | Danny Acuna's Blog
Great article.
Thanks!!
iam very thankful to you sir….
Glad that you liked it!!
Pingback: Claim based Authentication and WIF : Part 1 | Brij’s arena of .NET | Arash Tajalli